PLEASE_READ_ME: The Opportunistic Ransomware Devastating MySQL Servers
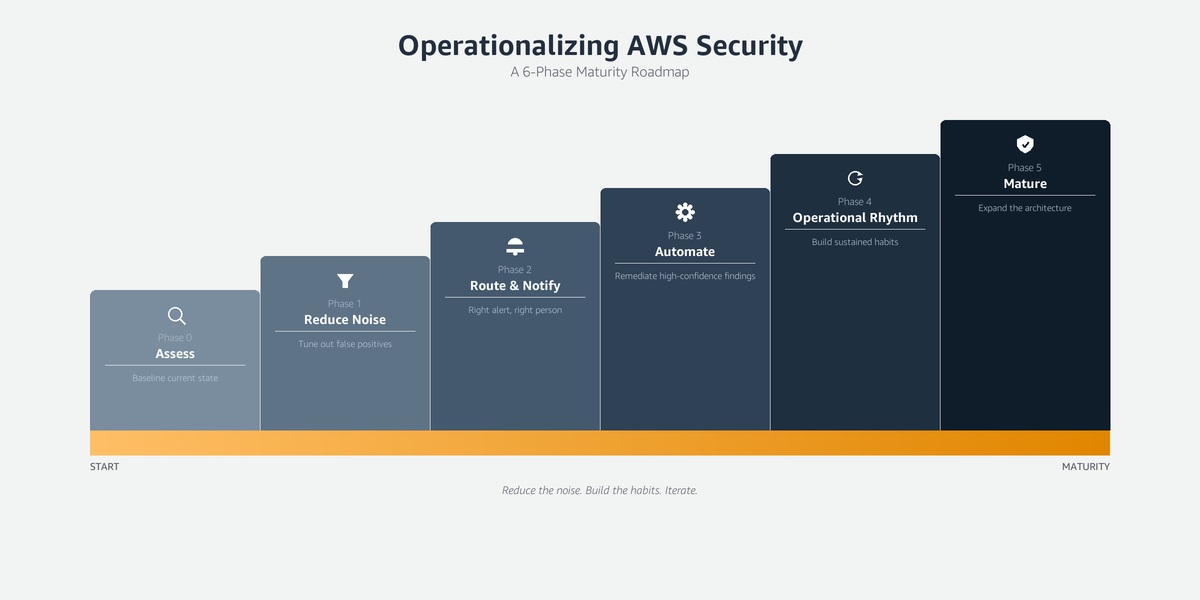
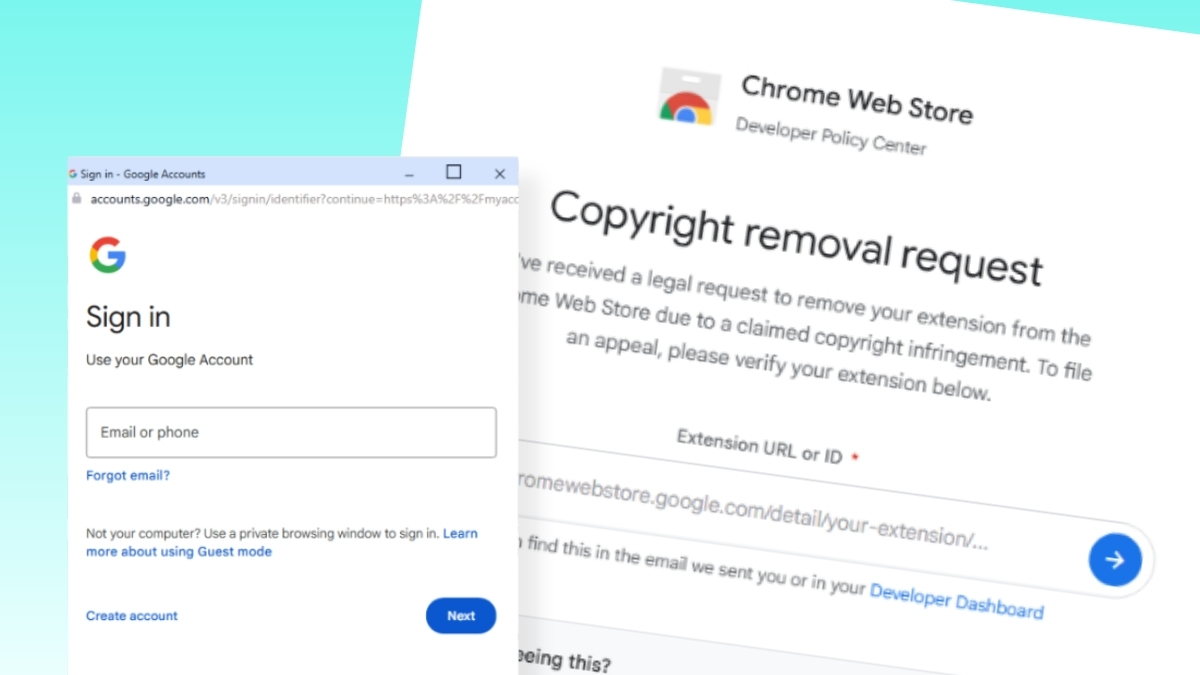
Guardicore Labs uncovers a Ransomware detection campaign targeting MySQL servers. Attackers use Double Extortion and publish data to pressure victims.